Featured Post
Every company has a finite number of engineering hours. This is not a philosophical statement. It’s a line item on your P&L, and it’s probably...
Latest Blogs
Abusix’s guide to cybersecurity, data trends, and expert insights.
Every company has a finite number of engineering hours. This is not a philosophical statement. It’s a line item on...
See How It Works Something remarkable is happening across Europe’s IT landscape. Governments, enterprises, and public institutions are actively migrating...
How Guardian Mail delivers rapid, measurable ROI by stopping threats at the edge before they ever reach your infrastructure. The...
Most organizations expect attacks at the application or endpoint level. Fewer are prepared for abuse that lives inside the network...
Blocklists remain one of the most effective controls in email security. They stop bad traffic early, reduce system load, and...
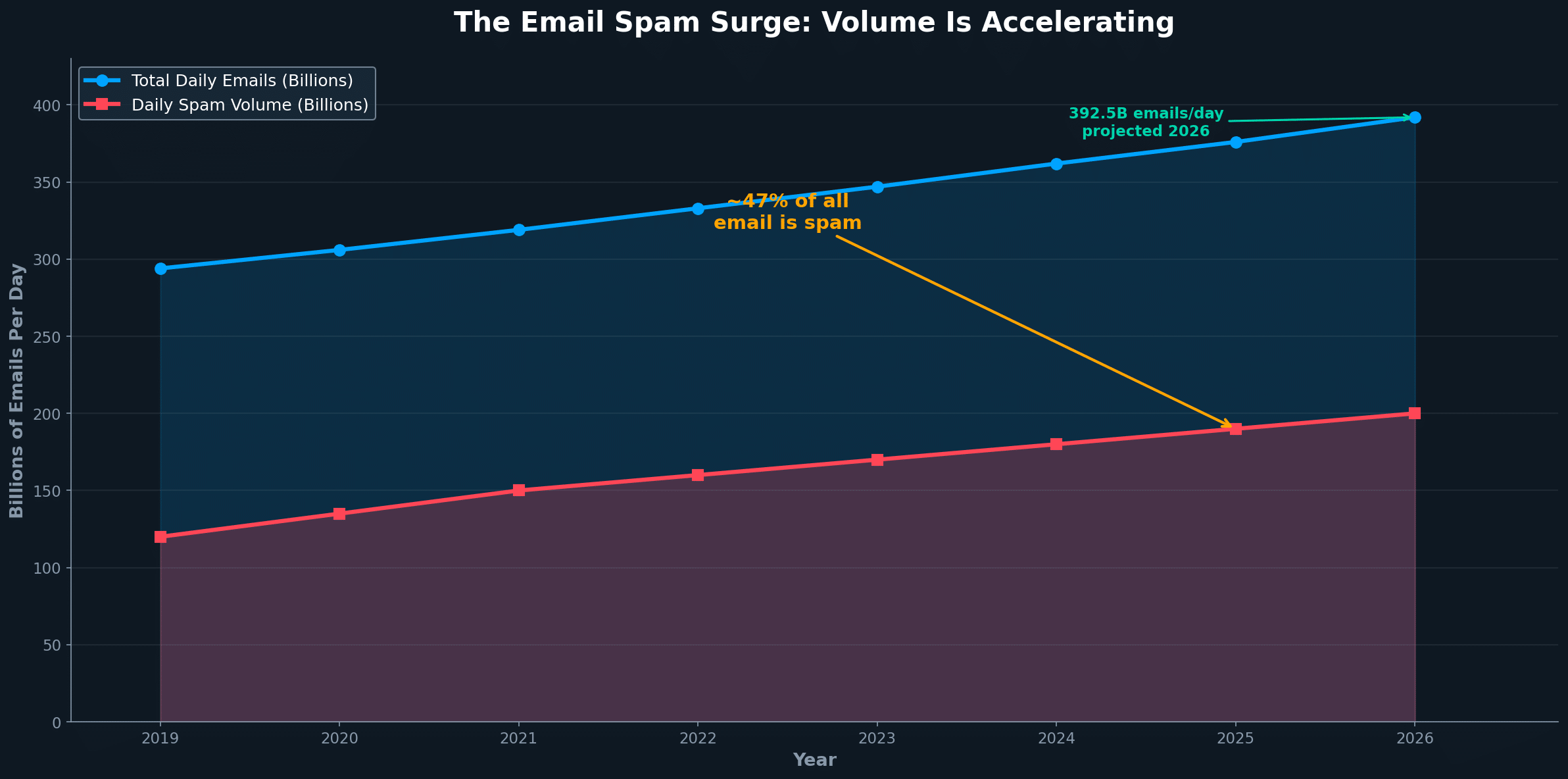
Most security conversations focus on content. What is inside the email. What the payload looks like. What the URL does....
Most security teams agree they need threat intelligence. Fewer agree on what “good” threat intelligence actually looks like. The market...
Mail platforms still lean heavily on blocklists, and that is a good thing. But the way blocklists are used has...
DNS queries are happening whether you notice them or not Every...
When people hear “network abuse,” they often think of spam. That...
Hosting providers see abuse every day. Phishing kits, <a class="glossaryLink" aria-describedby="tt"...
Ransomware attacks are no longer rare, targeted incidents. They are repeatable,...